Introduction: Why NIS2 is Not a "Paper Tiger"
The digital threat landscape has intensified dramatically in recent years. Cyberattacks are no longer just a problem for large corporations or state institutions. On the contrary: small and medium-sized enterprises (SMEs) are increasingly in the crosshairs of hacker syndicates because they often have fewer resources for IT security but still form critical parts of the supply chain.
The European Union has responded with the **NIS2 Directive** (Network and Information Security Directive 2). The goal is to create a uniformly high level of security for network and information systems across the EU. But what sounds like bureaucratic overhead to many entrepreneurs is, in reality, an essential necessity. NIS2 is not a paper tiger – the directive brings extensive obligations, draconian fines, and personal liability for management.
In this guide, you will learn everything you need to know about NIS2 as a medium-sized company: from applicability to technical requirements and a concrete roadmap for implementation.
"In 2026, cybersecurity is no longer an IT task, but a core strategic task for corporate management. NIS2 is the legal framework that now makes this unmistakably clear."
Chapter 1: Am I Affected? Checking the Thresholds
One of the most important aspects of NIS2 is the massive expansion of its scope. While the original NIS Directive primarily targeted "critical infrastructures" (KRITIS) such as energy providers or hospitals, NIS2 now covers large parts of the real economy.
The General Size Rule
In principle, companies are affected if they operate in one of the defined sectors and:
Employee Count
Employ at least **50 people**
Financial Scale
Annual turnover or balance sheet total over **€10 million**
A distinction is made between "Essential Entities" and "Important Entities." The former are subject to stricter oversight measures, but the technical minimum requirements are almost identical for both categories.
Caution: The Supply Chain Trap!
Even if your company is below the thresholds, you may be indirectly affected. Large corporations that fall directly under NIS2 are legally required to verify the security of their entire supply chain. This means: those who cannot demonstrate a NIS2-compliant security level risk being excluded as suppliers.
Chapter 2: The 10 Core Pillars of Risk Management
Article 21 of the NIS2 Directive lists the measures that every affected company must implement. These are defined as "state of the art" and include:
Systematic process for assessing cyber risks.
Clear plan for handling security incidents.
Backup strategies and emergency plans to maintain operations.
Assessing security measures of direct suppliers and service providers.
Security in acquisition, development, and maintenance of IT systems.
Use of modern encryption for sensitive data.
Regular awareness training for employees.
Mandatory use of MFA for all critical access points.
Control over access, data, and hardware assets.
Use of encrypted voice, video, and messaging solutions.
Chapter 3: Liability and Management Responsibility
This is the point that makes NIS2 so relevant for SMEs: responsibility can no longer be completely delegated to the IT manager or an external service provider. Management must not only approve the cybersecurity measures but also **supervise** their implementation.
In the event of violations, the directive provides for significant fines:
Essential Entities
Sectors with high criticality
Up to €10 Millionor 2% of total worldwide annual turnover.
Important Entities
Other critical sectors
Up to €7 Millionor 1.4% of total worldwide annual turnover.
In addition, managing directors can be personally liable with their private assets in the event of culpable neglect of their duty of supervision. A training obligation for management bodies is also explicitly anchored in the directive.
Chapter 4: Reporting Obligations in Record Time
If a "significant security incident" occurs, companies must react extremely quickly. The legislator provides for a multi-stage process:
**Early Warning**: Initial notification of a significant incident to the national authority (e.g., BSI in Germany).
**Incident Report**: More detailed analysis and initial assessment of the impact.
**Final Report**: Comprehensive documentation of causes and countermeasures taken.
Without a functioning monitoring system (e.g., a SOC - Security Operations Center), these deadlines are almost impossible for SMEs to meet.
Chapter 5: The 5-Step Roadmap to NIS2 Compliance
How do you get started? We recommend the following approach:
-
Status-Quo Analysis
Conduct a gap audit. Where do you stand today compared to the requirements?
-
Asset Management
Create a complete inventory of all IT systems, data, and suppliers.
-
Technical Upgrade
Implement quick-wins like MFA, encrypted backups, and patch management.
-
Process Design
Develop emergency manuals and define responsibilities for reporting processes.
-
Employee Training
Make cybersecurity part of the corporate culture.
Conclusion: Seeing NIS2 as an Opportunity
Yes, NIS2 involves effort. But consider it an investment in the resilience of your company. A cyberattack can ruin an SME – compliance with NIS2 requirements protects you from it. In addition, cybersecurity is increasingly becoming a selling point. Customers and partners prefer companies that demonstrably operate securely.
Pragma-Code supports you every step of this journey. From the initial analysis to the operation of AI-powered security monitoring, we are your partner for the modern SME.
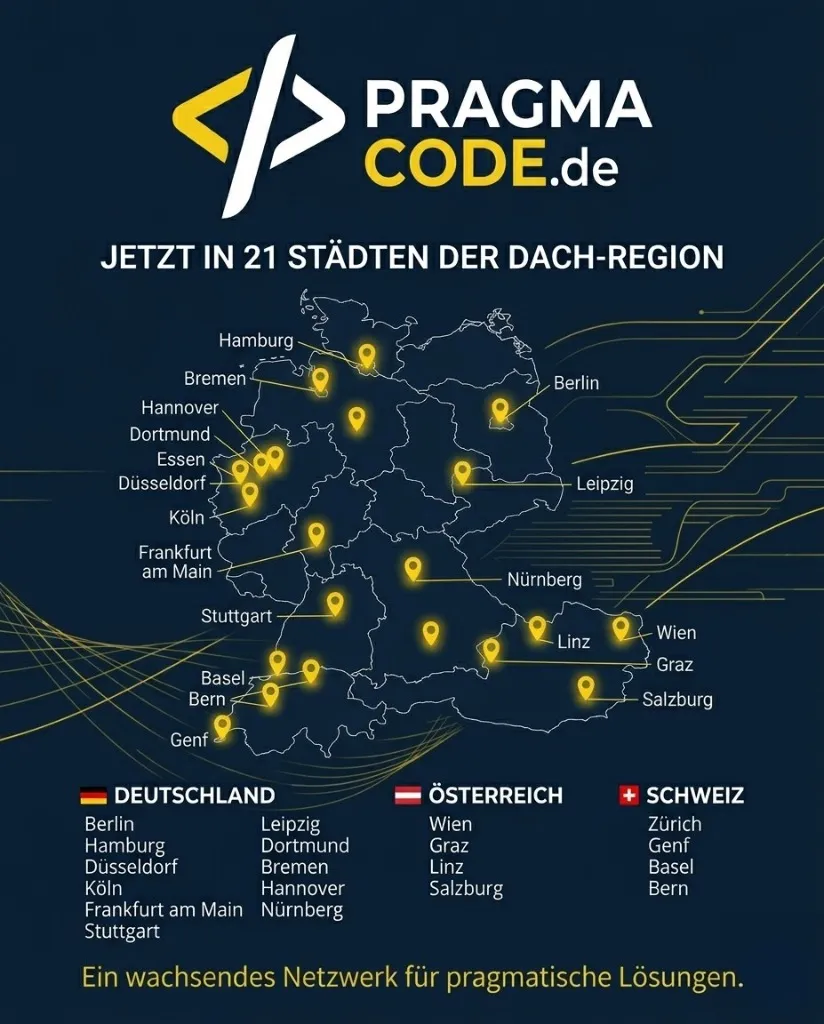
Our Regional Expertise
We are your digital partner – regionally anchored and successfully scaling across borders.
Is Your Company Ready for NIS2?
Let's check together how we can take your cybersecurity to the next level and position you for legal security.
Book your free strategy call nowExtended Specialized Glossary
NIS2 Directive
The "Network and Information Security Directive 2" is an EU law to strengthen cybersecurity in critical sectors.
Essential Entities
Sectors with high criticality (e.g., energy, health) that are subject to stricter controls.
Important Entities
Sectors such as mechanical engineering, food, or digital services that are also NIS2-obligated.
Multi-Factor Authentication (MFA)
A security process in which users must provide two or more different factors for identification.
Business Continuity Management (BCM)
A management process designed to ensure that business processes can be continued even in crisis situations.